
Alternatives to Permit MCP Gateway
Passerelle de sécurité MCP que les développeurs adorent et que les RSSI approuvent
Discover the 9 best alternatives to Permit MCP Gateway in the securite category.

OpenObserve
Open-source native AI observability platform, alternative to Datadog
Fast, scalable, and cost-effective open-source observability platform. Monitor logs, metrics, and traces with storage costs 140 times lower than ElasticSearch. Get started in 2 minutes.
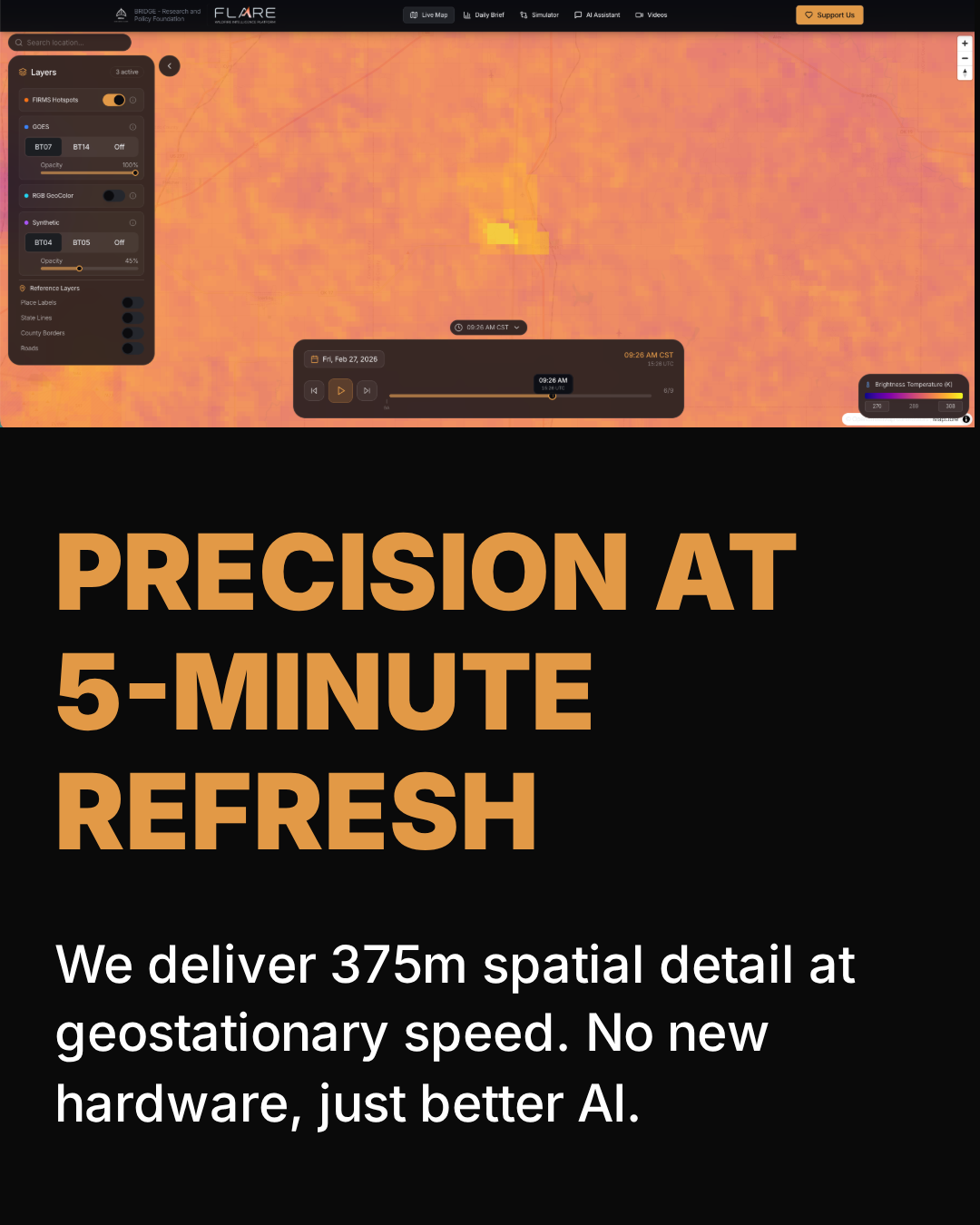
FLARE
Wildfire intelligence ready for decision-making
Utilities lose infrastructure. Insurers recalculate regions. Agencies arrive too late. The same cause every time: resolution and refresh frequency have never been combined—until now. FLARE delivers a 375m FireScore every 5 minutes via geostationary satellites, covering the entire continental United States. The FireScore detects wildfires earlier than existing tools and tracks their progression continuously, not just isolated hotspots. A daily 375m risk index, 15-day forecast, and mitigation simulator are coming soon.

Aegis AI
AI safety supervisor for construction sites
Aegis AI is an autonomous AI safety supervisor designed for construction sites. Unlike traditional systems that only detect objects, Aegis understands site context through multimodal AI. It analyzes video feeds, identifies dangerous behaviors, and triggers real-time alerts before an incident occurs. Works with existing cameras—no new hardware required. Key features: real-time risk detection, contextual site monitoring, instant alerts for hazardous activities, multi-camera visibility.
Agumbe LLM Gateway (and Console)
Control and traceability of enterprise AI for enhanced security
Most LLM safeguards fail in production. Agumbe LLM Gateway lets you define and enforce application-level safeguards in real-time request flows. Detects, masks, or blocks prompt injections (direct and indirect), sensitive data (PII, secrets), forbidden topics, and verifies response safety and relevance—all while respecting budget constraints (economic models for development, premium models reserved for production). Fully testable via a console using the same gateway as the production environment.

Banyan AI Lite
AI-powered SaaS churn detection and prevention
Churn is the biggest challenge for SaaS companies, affecting up to 50% of them. Banyan AI helps detect churn risks before they occur and prevent them. The tool unifies your critical data (CRM, billing, support, product usage) in a single interface to identify risks and expansion opportunities. Implementation time: a few minutes. Measurable and quantifiable results.

Sonarly
AI that autonomously fixes production issues
Connect Sentry, Datadog, or any other monitoring tool. Sonarly's agents sort your alerts, eliminate noise, and fix bugs with full context from your production system—autonomously! Most monitoring tools tell you what broke. Sonarly explains why, groups duplicates, and provides a ready-to-use PR with supporting evidence. Powered by Claude Code and Opus 4.6, with deep production context enhanced by Sonarly.

Hackerdogs.ai
See your organization through the eyes of hackers
We provide actionable intelligence at a CIA-level in real-time to help you make informed, evidence-based decisions to secure your business. We invented ATEM - Autonomous Threat Exposure Management. We show you the same view a hacker has of your organization from the outside. We don’t need much information from you because we actively collect it for your security.

deepidv
Native AI-powered verification and anti-fraud engine
deepidv is the native AI identity verification engine designed from the ground up — without third-party APIs or markup. Verify ID documents, continuously monitor, deploy risk agents, precisely detect deepfakes, perform credit checks, background checks, title searches, and validate addresses in 211+ countries. Enterprise-grade power with startup-friendly pricing.

LaunchSafe
AI agents that test your application's security and prove real vulnerabilities
LaunchSafe offers agentic pentesting in just a few clicks. Its AI agents actively attempt to hack your application, both at the code and production environment levels, to identify real vulnerabilities. Unlike pentests costing over $10,000 that take weeks or scanners generating false positives, LaunchSafe proves exploits in ~3 hours with OWASP Top 10 coverage. Issues are verified by certified cybersecurity engineers, and its Remediation Plan can automatically submit PRs to resolve them. Designed for startups and teams that deliver quickly.